Snapshots of the experimental sites captured by the wireless spy camera. | Download Scientific Diagram
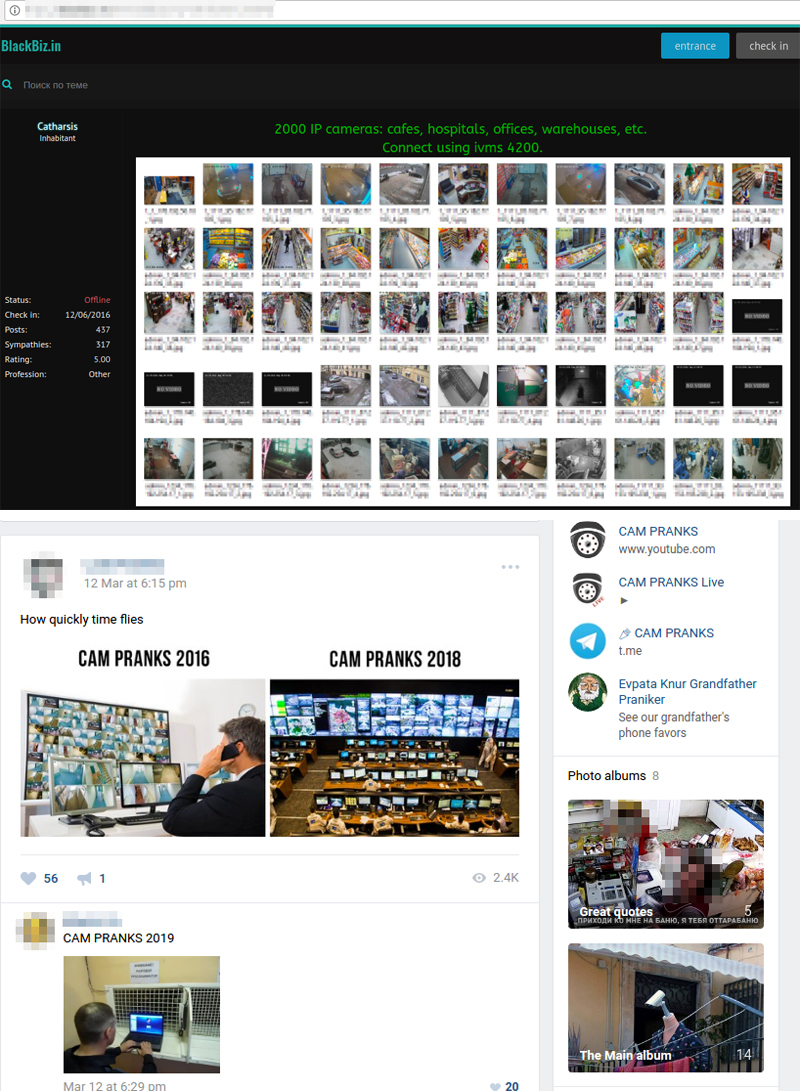
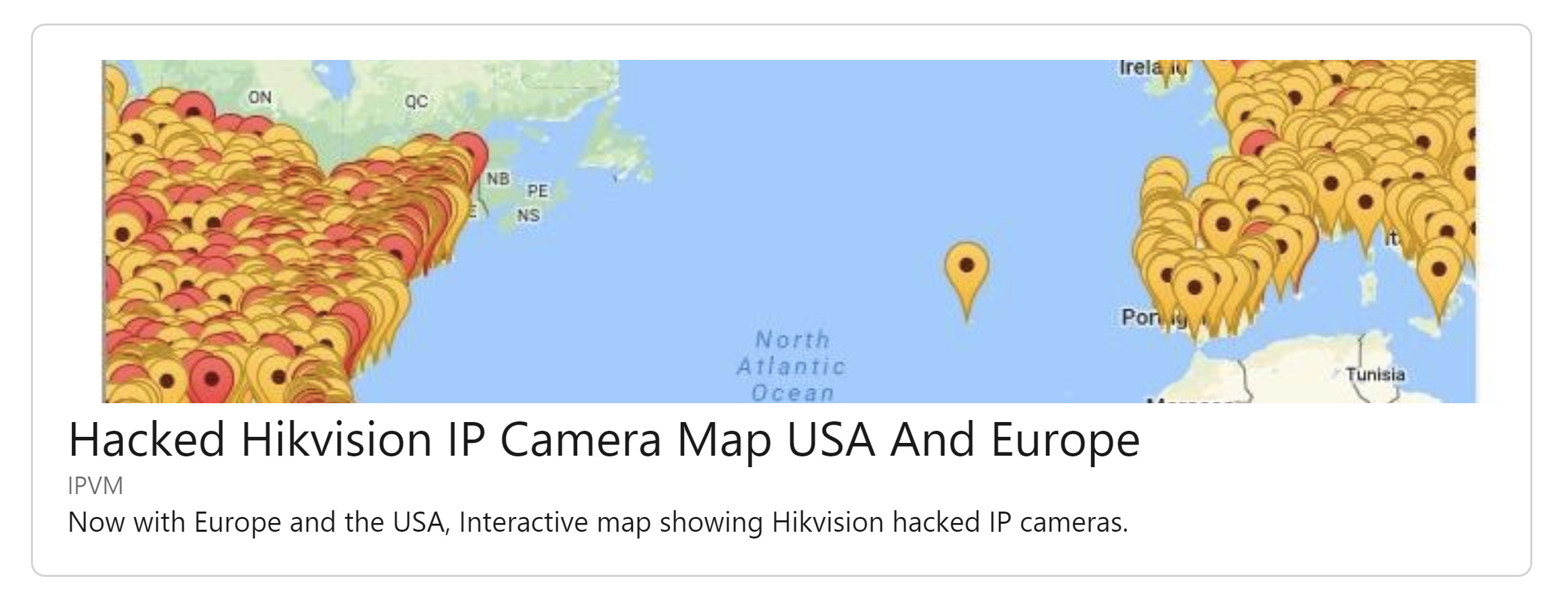
Exposed Video Streams: How Hackers Abuse Surveillance Cameras - Nouvelles de sécurité - Trend Micro FR

Over 55,000 security camera DVRs are vulnerable to an exploit so simple it fits in a tweet - Boing Boing

David Bombal on X: "Hacking CCTV and IP cameras YouTube video: https://t.co/3oBOV17dT3 #cyber #hacking #hack #cctv #camera #infosec #cybersecurity #pentest #pentesting #hackers #ukraine @three_cube https://t.co/tSdum1V8eT" / X

Is your webcam a Trojan Horse for hackers, voyeurs and spies? Hundreds of Hong Kong households seen by strangers online via Shodan search engine | South China Morning Post

Lights, Camera, HACKED! An insight into the world of popular IP Cameras | NCC Group Research Blog | Making the world safer and more secure